B) False
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Many businesses use ____ to limit employees' Web access.
A) content filtering
B) Web bugs
C) honeypots
D) spyware
F) B) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Symptoms of a user with computer addiction include all of the following except ____.
A) craves computer time
B) unable to stop computer activity
C) neglects family and friends
D) irritable when at the computer
F) C) and D)
Correct Answer

verified
Correct Answer
verified
True/False
To remove spyware, users need to obtain a special program that can detect and delete it.
B) False
Correct Answer

verified
Correct Answer
verified
True/False
Undervoltages can cause equipment damage, but generally do not cause data loss.
B) False
Correct Answer

verified
Correct Answer
verified
Multiple Choice
With a three-generation backup policy, the grandparent is the ____.
A) most recent copy of the file
B) second oldest copy of the file
C) oldest copy of the file
D) original file
F) A) and B)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A ____ is a mathematical formula that generates a code from the contents of an e-mail message.
A) spike
B) macro
C) password
D) hash
F) B) and D)
Correct Answer

verified
Correct Answer
verified
True/False
Personal firewalls constantly monitor all transmissions to and from a computer and inform users of any attempted intrusion.
B) False
Correct Answer

verified
Correct Answer
verified
True/False
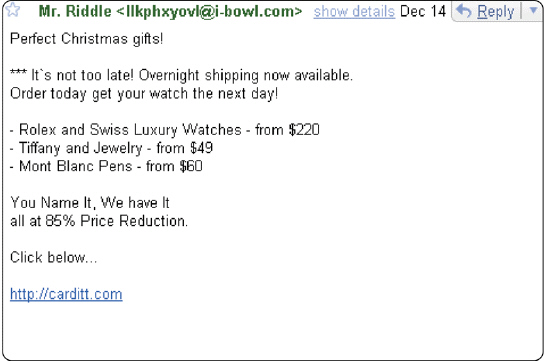 Figure 11-1 A message like the one in Figure 11-1, when sent through an instant messaging service, is called spit .
Figure 11-1 A message like the one in Figure 11-1, when sent through an instant messaging service, is called spit .
B) False
Correct Answer

verified
Correct Answer
verified
Multiple Choice
To help reduce the chance of ____, physical controls such as locked doors and cables usually are adequate to protect equipment.
A) software piracy
B) hardware theft
C) system failure
D) unauthorized access
F) C) and D)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A certificate ____ is an authorized person or company that issues and verifies digital certificates.
A) authority
B) agency
C) office
D) bureau
F) None of the above
Correct Answer

verified
Correct Answer
verified
True/False
To utilize intrusion detection software requires little expertise because the programs are simple and easy to use and interpret.
B) False
Correct Answer

verified
Correct Answer
verified
True/False
It is illegal for employers to use software programs that monitor employees.
B) False
Correct Answer

verified
Correct Answer
verified
Short Answer
A spyware program communicates information it collects to some inside source while a user is ____________________.
Correct Answer

verified
Correct Answer
verified
Multiple Choice
The ____ is the destructive event or prank a malicious-logic program is intended to deliver.
A) zombie
B) hash
C) cracker
D) payload
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Computer viruses, worms, and Trojan horses deliver their payload on a computer when a user ____.
A) opens an infected file
B) runs an infected program
C) boots the computer with an infected disk in a disk drive
D) all of the above
F) B) and C)
Correct Answer

verified
Correct Answer
verified
True/False
A cyberextortionist uses the Internet or network to destroy or damage computers for political reasons.
B) False
Correct Answer

verified
Correct Answer
verified
Short Answer
A more devastating type of DoS attack is the ____________________, in which multiple unsuspecting computers are used to attack multiple computer networks.
Correct Answer

verified
Correct Answer
verified
Multiple Choice
Critical Thinking Questions Case 1 One form of software theft is the theft of the software from software manufacturers, which is known as piracy. Because this has historically been rather easy to do, the practice has become very common. As a computer instructor you feel it is your responsibility to explain this practice to students through the use of some examples. Which of the following practice IS permissible under a EULA?
A) Ahmed rents his copy of Adobe Illustrator.
B) The lab administrator at the college installs Fireworks on the school computer lab network.
C) Karen installs Flash on one desktop computer and one notebook computer.
D) Perry gives a copy of Microsoft Publisher 2007 to his friend, while continuing to use the software.
F) All of the above
Correct Answer

verified
Correct Answer
verified
Multiple Choice
A(n) ____ is a device that contains surge protection circuits and one or more batteries that can provide power during a temporary or permanent loss of power.
A) PGP
B) DoS
C) UPS
D) DDos
F) A) and C)
Correct Answer

verified
Correct Answer
verified
Showing 21 - 40 of 191
Related Exams